Articles By This Author
Configuring Amazon S3 Access Keys Securely for UpdraftPlus (WordPress)
Using Amazon Web Services S3 as remote storage for UpdraftPlus is a common and reliable approach for backing up a WordPress site.However, many users are confused when AWS warns against long-term access keys and suggests alternative authentication methods. This article explains the correct and secure way to configure S3 access for UpdraftPlus, why AWS shows […]
Aliexpress : The Bundle Deal Problem
Tired of AliExpress forcing you into “Bundle Deals” when you just want to buy a single item? This free userscript intercepts those sneaky links and redirects you straight to the actual product page. The Bundle Deal Problem AliExpress has been increasingly pushing shoppers toward “Bundle Deals” — grouped offers that look attractive but prevent you […]
Artificial Intelligence and the Personal Computer: A Valid Comparison, but an Incomplete One
As artificial intelligence (AI) systems rapidly improve and spread across industries, a common argument emerges: the AI shift is comparable to the rise of the personal computer (PC) in the 1980s and 1990s. According to this view, AI represents another technological wave—initially disruptive, eventually normalized—requiring adaptation rather than concern. While this comparison is not without […]
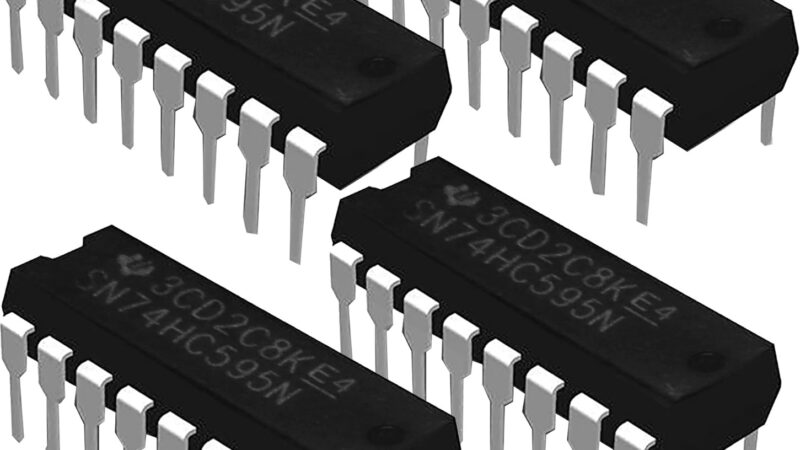
SIPO and PISO shift registers with Arduino and ESP (ESP8266 / ESP32)
When working with Arduino, ESP8266 or ESP32, you quickly hit a simple limit: not enough GPIO pins.Instead of stacking boards or using complex expanders, there is a very clean and proven solution: shift registers. The two main types are: Why use shift registers? With only 3 pins, you can manage 8, 16, 32+ inputs or […]
Evaluating iSCSI vs NFS for Proxmox Storage: A Comparative Analysis
In the realm of Proxmox virtualization, the choice between iSCSI and NFS storage protocols is crucial. iSCSI offers the speed and efficiency of block-level storage, ideal for high-performance needs, yet demands meticulous setup and network tuning. NFS, with its straightforward setup and file-level simplicity, excels in ease of use and flexibility, perfect for environments requiring shared file access. Balancing these factors—performance, scalability, management ease, and security—guides IT professionals in making an informed decision that best fits their virtual infrastructure’s unique demands.
How to Resolve Proxmox VE Cluster Issues by Temporarily Stopping Cluster Services
Navigating the complexities of Proxmox VE cluster management? Discover a reliable method for safely implementing configuration changes by temporarily halting cluster services. This guide offers a step-by-step approach, detailing how to stop the pve-cluster and corosync services and utilize the Proxmox configuration filesystem daemon in local mode. Ideal for administrators seeking controlled updates in their Proxmox environments, this strategy ensures modifications are made safely, without disrupting cluster synchronization.
AWS – Key Differences Between Network Access Control Lists (NACLs) and Security Groups
Navigating the complexities of cloud security requires a deep understanding of the tools at your disposal. Two fundamental components—Network Access Control Lists (NACLs) and Security Groups—serve as the cornerstone of network security in cloud environments. While both are instrumental in safeguarding your resources, they differ significantly in their operation and application. NACLs provide a layer of defense at the subnet level, controlling traffic based on a set of ordered rules. Security Groups, conversely, offer a more granular level of protection, applying to individual instances with a stateful approach to traffic filtering. This article elucidates the key differences between NACLs and Security Groups, shedding light on their unique roles and how they complement each other in fortifying your cloud infrastructure.
Unlocking Data Transformation with DBT: A Comprehensive Guide
Explore the transformative power of DBT (Data Build Tool) in the modern data landscape. This comprehensive guide delves into how DBT revolutionizes data transformation, making it an essential tool for data analysts and engineers. Discover its key features, including version control, testing, and documentation, and learn how its implementation can streamline data workflows across various industries. Join the DBT revolution and step into a future where data transformation catalyzes growth and innovation.